Secure KVM Isolators
Isolator models addressed on this page:
- FI11H-M – Secure 1-Port HDMI KVM Isolator
- FI11PH-M/MT – Secure 1-Port DisplayPort/HDMI KVM Isolator
Accessories: Accessories for centralized installations:
- RK-4U-HKS-10 – RackMount KIT 4U – The RK−4U−HKS−10 enables mounting up to 10 Isolators in a 19″ 4U rack space.
- 1U 6 Isolators kit – RK-1U6-FV/I11H/PH-M includes HSL’s PDUI12, power distribution unit and 6 Isolators installed in a specially designed chassis for mounting in a network cabinet.
- Power Distribution Unit for Isolators – PDUI – Enables connecting multiple Isolators (and other HSL 12V-powered devices) to computers in a rack without additional external power supply outlets.
——————————————————————————-
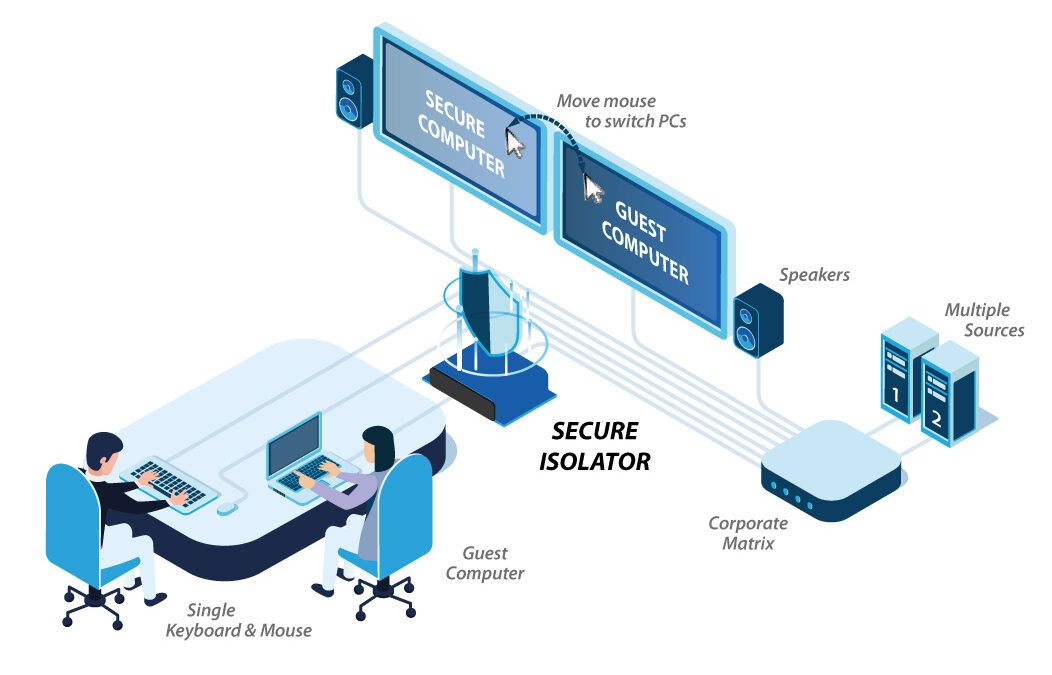
The secure isolator prevents vulnerable peripherals from mediating between compromised and secure computers by ensuring that video, audio and USB data flows in a single direction. By preventing host-to-peripheral direct access, the secure isolator eliminates data leakage.
The secure isolator provides the highest possible computer & peripheral isolation as demanded by government agencies, military, financial institutions and similar security sensitive customers.
The isolator perfectly suits scenarios where vulnerable peripherals or computers may impose a security threat. For example, in a secure meeting room, when an unsupervised (non-secure) guest laptop connects to a projector shared with a classified computer. By isolating the classified computer from the projector, the secure isolator protects the classified computer from being infected by the guest computer by exploiting a projector vulnerability.
To prevent bi-directional communication via the EDID channel, numerous mechanisms were set forth to protect EDID transactions:
-
- EDID is read from the display only when the user presses the EDID capture button, typically during installation. This prevents continuous EDID transformation between the display and the source.
- EDID information is parsed to assure that only legitimate information is passed between the display and the source. The Isolator is used as a buffer to protect against transferring malicious through the EDID channel.
- EDID information is limited to the basic essentials. Instead of passing the full EDID and MCCS, HSL’s Isolators limit the EDID to the minimum required.
Additionally, by permitting sound to travel only in one direction from the PC to the speaker, the isolator protects against eavesdropping attempts by preventing intruders from compromising a computer’s security and re-tasking the audio line-in (headset/speaker) into a microphone line. The embedded digital audio via HDMI/DP is also protected due to unidirectional video transfer.
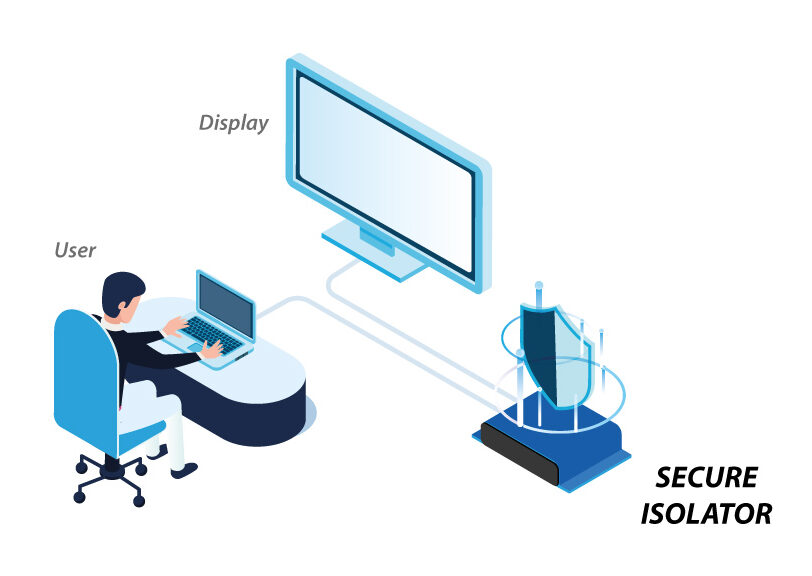
Easy Installation
-
- Connect the computer’s USB keyboard & mouse and display ports to the Isolator.
- Connect the isolator to the keyboard, mouse, display and audio peripherals.
- Computer and peripherals are fully isolated from each other.
- User can now securely use the peripherals.
Running an EDID Capture
Before using the isolator, run a one-time EDID capture. This prevents the continuous transfer of potentially malicious data – from the display to the PC – that could infect the PC, cause data leakage, and so on.
Preparation:
- Connect the PC and all peripherals to the unit.
- Make sure the PC, display, and unit are ON.
To run an EDID capture:
- Short-click the EDID LOCK button – for less than one second.
At first, the EDID LED flickers for a few seconds and then lights continuously. If the EDID LED is OFF, repeat the procedure.
Warning: Long-clicking the EDID LOCK button sends the unit into an undesired loop. If this happens, restart the unit and repeat the procedure. - Restart the unit.
Note: The procedure needs to be performed for new installations and when changing a display.
Certified for NIAP Common Criteria PP4.0 PSD Protection Profile
MODELS
SPECIFICATIONS
DOWNLOADS
RELATED PRODUCTS
You may also like…
-
KVM Cables
This product has multiple variants. The options may be chosen on the product page -
Power Distribution Unit for Isolators – PDUI
This product has multiple variants. The options may be chosen on the product page -
Secure Video Isolators
This product has multiple variants. The options may be chosen on the product page